7 Common Errors in Secure IT Asset Disposal (And Their Solutions)
For IT directors and data centre managers, the end of a hardware lifecycle is often seen as a logistical headache rather than a security priority. However, treating decommissioned hardware as “trash” is a high-stakes gamble. In 2026, with data regulations becoming more stringent and the value of enterprise hardware shifting rapidly, your secure IT asset disposal strategy is either a shield or a massive liability.
Data breaches via discarded hardware are not just a theoretical risk; they are a frequent reality for organisations that cut corners. From unwiped SSDs to undocumented chain-of-custody gaps, the “out of sight, out of mind” approach leads to GDPR fines, reputational damage, and missed sustainability targets.
At Flux IT Hardware, we help businesses navigate the complexities of ITAD services in the UK. Here are the seven most common mistakes we see companies make and exactly how you can fix them.
❌ Mistake 1: The “Delete and Format” Myth
Many IT teams still believe that a simple factory reset or a quick format is enough to “clear” an enterprise server or storage array. It isn’t. Professional data recovery tools can easily reconstruct data from drives that haven’t been properly sanitised.
⚠️ The Risk: Critical Data Leaks
Client databases, proprietary software, and internal network configurations remain accessible even after a drive appears empty. If that drive enters the secondary market, your company’s “crown jewels” go with it.
✅ The Fix: Certified Data Sanitisation
Use industry-standard data destruction methods. This means software-based wiping that follows NIST 800-88 guidelines or physical destruction (shredding) for drives that are end-of-life.
- Action: Always demand a Certificate of Data Destruction for every single serialised asset.
- Resource: If you are clearing out more than just drives, check our FAQ on clearing out full infrastructure.
❌ Mistake 2: Lacking a Formal ITAD Policy
Disposing of assets on an “ad-hoc” basis: whenever the cupboard gets too full, is a recipe for disaster. Without a documented process, different departments will handle hardware differently, leading to inconsistencies in security and compliance.
⚠️ The Risk: Compliance Failures
During an audit, “we usually send it to a local recycler” is not a valid compliance answer. You need a paper trail that proves a consistent, secure methodology was followed.
✅ The Fix: Standard Operating Procedures (SOPs)
Develop a comprehensive ITAD policy that outlines:
- Which assets are subject to disposal.
- Who is authorised to initiate the disposal.
- The specific destruction methods required for different data classifications.
- The frequency of disposal cycles.
❌ Mistake 3: Poor Inventory Management and “Ghost Assets”
If you don’t know exactly what you have, you can’t be sure it was disposed of securely. “Ghost assets” are items that remain on your books but have physically left the building: or worse, items that are sitting in an unlocked corridor waiting for pickup.
⚠️ The Risk: Physical Theft
Hardware sitting in unsecured areas is a prime target for theft. If a server goes missing before it reaches the ITAD provider, you have no way of proving the data on it was secure.
✅ The Fix: Lifecycle Tracking
Maintain a live asset register. Every item should be scanned at the point of decommissioning and cross-referenced against the ITAD provider’s manifest.
- Tip: Identify high-value items early. Some brands, like Cisco or HP, hold significant resale value. See which server brands are most valuable to help offset your disposal costs.
❌ Mistake 4: Prioritising Lowest Cost over Provenance
It is tempting to go with the cheapest disposal option, or even a “free” service. However, in the world of ITAD services UK, if you aren’t paying for the service, the provider is likely making their money by cutting corners on security or environmental compliance.
⚠️ The Risk: Environmental and Legal Liability
Illegal e-waste dumping is a major global issue. If your branded hardware is found in an illegal landfill, the environmental fines and PR backlash will land on your doorstep, not the shady vendor’s.
✅ The Fix: Partner with Certified Experts
Work with a partner who prioritises the circular economy. At Flux IT Hardware, we integrate our sustainability policy into every disposal project, ensuring that hardware is either refurbished for reuse or recycled according to strict WEEE regulations.
❌ Mistake 5: Neglecting the Chain of Custody
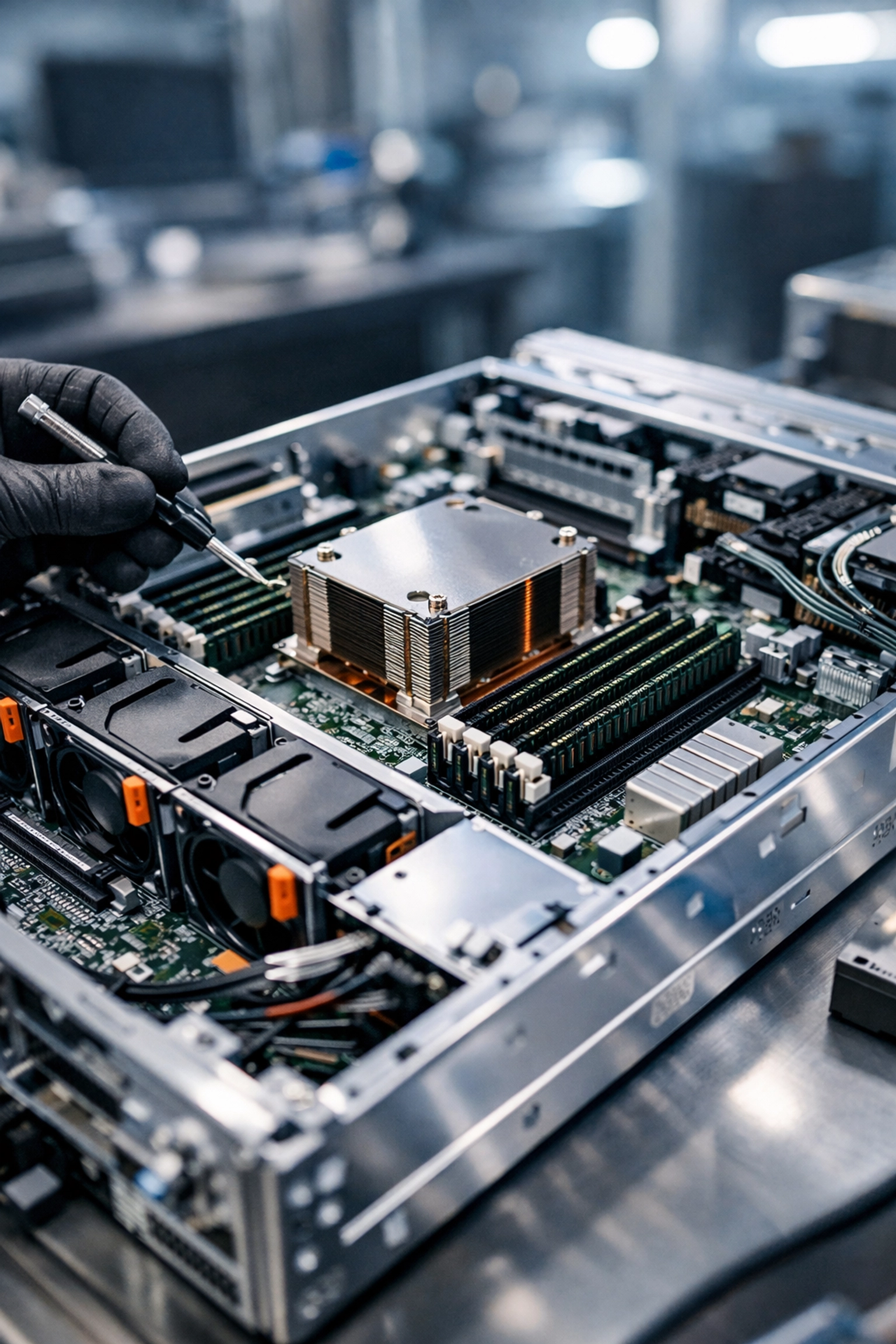
The most vulnerable moment for your data is the “transit gap”: the time between the hardware leaving your rack and arriving at the processing facility.
⚠️ The Risk: Interception During Transit
Unmarked vans, lack of GPS tracking, and multiple hand-offs between couriers create opportunities for hardware to “disappear.”
✅ The Fix: Secure Logistics
Ensure your ITAD provider uses vetted drivers and secure, sealed vehicles. For high-security environments, consider on-site data destruction where drives are shredded before they even leave your building. This eliminates the transit risk entirely.
❌ Mistake 6: Ignoring the “Human Variable”
We often focus on the tech, but the people handling the hardware are the biggest risk. Internal staff who aren’t trained in secure decommissioning might accidentally leave a console cable attached, or worse, leave a “sticky note” with credentials on a chassis.
⚠️ The Risk: Insider Negligence
Even well-meaning employees can cause a breach by not following protocol.
✅ The Fix: Employee Training and Awareness
Educate your IT team on the importance of secure IT asset disposal. Treat the decommissioning process with the same level of security as you do your live cybersecurity and firewall management.
❌ Mistake 7: Failing to Conduct Regular Audits
Setting up an ITAD process is not a “one and done” task. Regulations change, technology evolves (e.g., the shift from HDD to NVMe requires different wiping protocols), and vendor standards can slip.
⚠️ The Risk: Process Decay
An ITAD strategy that worked in 2022 may be woefully inadequate for the hardware landscape of 2026.
✅ The Fix: Annual Reviews
Audit your ITAD partner at least once a year. Review their certifications, visit their facility if possible, and check their latest return and warranty policies to ensure they still meet your enterprise standards.
Why ITAD is a Sustainability Win
Secure disposal isn’t just about risk: it’s about opportunity. The most sustainable server is the one that stays in the circular economy. By choosing professional ITAD services UK, you aren’t just destroying data; you are enabling the refurbishment of components.
When you decommission older equipment, such as Cisco EOSL hardware, Flux IT Hardware can often find a second life for these units. This contributes directly to your corporate ESG (Environmental, Social, and Governance) targets by:
- Reducing e-waste.
- Lowering the carbon footprint of new manufacturing.
- Providing affordable tech to secondary markets.
How Flux IT Hardware Can Help
Navigating the transition from “active asset” to “securely disposed” requires a partner who understands the hardware inside the box, not just the box itself.
At Flux IT Hardware, we provide a seamless decommissioning service that covers:
- Asset Recovery: Get cash back for your used Cisco switches or Juniper equipment.
- Secure Data Destruction: Certified wiping and physical shredding.
- Compliance: Full documentation and certificates for every project.
- Repairs: We can even offer enterprise IT repairs to extend the life of your current fleet before you decide to dispose.
🏁 Final Thought: Don’t Wait for a Breach
The cost of professional secure IT asset disposal is a fraction of the cost of a data breach. If your current server room looks like a hardware graveyard, it’s time to act.
Ready to secure your data and hit your sustainability goals?
Contact Flux IT Hardware today for a consultation on your next decommissioning project. Let’s turn your EOL hardware into a secure, sustainable success story.
What do we buy?
| Cisco Equipment | Aruba Equipment | AI Hardware |
| HPE Equipment | Server Equipment | NVIDIA H100 & A100 AI GPUs |
| Juniper Equipment | Corporate Desktops & Laptops | Barcode Scanners |